Hubbing out involves placing a hub or something like a Throwing Star lan tap between a host and switch. Per the books, in most situations duplex of target is cut to half.
View->Coloring Rules is a handy way to add your own rules to make traffic stand out.
Mark a packet so it stands out with white text & black backdrop. CTRL+M and you can advance or reverse with ctrl-shift-n and ctrl-shift-b.
You can merge pcaps. Tie together captures from multiple devices to get a better view. File-> Merge
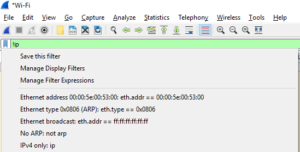
Create capture and display filters. Wireshark uses comparison and logical operators.
Comparison Operators
== equal to != not equal to > greater than < less than >= greater than or equal to <= less than or equal to
Logical Operators
and both conditions must be true or either one of the conditions must be true xor one and only one condition must be true not neither one of the conditions is true
Sample Filter Expressions
host www.biokode.net display all traffic from host www.example.com !ip display all non IP traffic ip.dst==192.168.1.1 Display all traffic with a destination of 192.168.1.1
You can manage and apply existing filters, or create a new filter from a current expression from within the filter construction dialog by clicking on the small filter icon to the left of the filter expression icon within the filter toolbar!
Name Resolution
You can enable name resolution by opening the Capture Options dialog. Capture–> Options and then select Options tab.
- MAC Name Resolution – Uses ARP to convert layer 2 MAC address into layer 3 IP addresses; display 00:11:22:33:44:55:66 as 192.168.1.7.
- Network Name Resolution – Uses DNS to resolve IP addresses to human readable DNS names; display 192.168.1.7 as SalesWorkstation001.
- Transport Name Resolution – Convert port number to associated transport technology; display port 80 as http.
Name resolution may not be desirable. It can add processing overhead and resolution can fail. A capture does not store name resolution data, so expect this overhead when reviewing previously saved captures.
Protocol Dissection
Wireshark relies on protocol dissectors to to convert raw data into something understood by Wireshark, but it can select the wrong protocol dissector. Most commonly this occurs when a standard protocol is using a non-standard port. For instance, HTTP traffic flowing over port 22 could be classified as SSH!
Right click on a packet and from the menu select “Decode As.” This enables you to select a different protocol dissector than that which was chosen by Wireshark.
Following TCP Streams
Right click on a packet in the Packet list pane of the main window to Follow->TCP Stream and view related packets and their payload that is delivered to the application level in the OSI stack. You can also select a TCP packet in the TCP tab of the Statistics->Conversations dialog.
Endpoints
Statistics->Endpoints summarizes traffic measured in bits, bytes, and packets grouped by hosts.